
In the wild west of Decentralized Finance (DeFi), you're either proactive about safety or you're exit liquidity. A solid protocol safety analysis is the framework you use to spot vulnerabilities before they drain your portfolio. This isn't about reacting to the latest multi-million dollar exploit; it's about systematically assessing risk.
Honestly, it's the one thing that separates sustainable yield farmers from those who suffer catastrophic losses.
Why Protocol Safety Analysis Is Your Best Defense in DeFi
If you want to survive and actually thrive in DeFi, you have to do more than just chase the highest APY. It requires a complete mental shift towards rigorous risk management. Think of it less as a technical chore for developers and more as an essential survival strategy for every single investor. It means digging into a project's technical guts, its economic model, and how the whole thing is run.
The goal here is to uncover the hidden dangers that aren't screaming at you from a protocol's flashy marketing page or its Total Value Locked (TVL). By taking this approach, you start asking the right questions:
Are the smart contracts actually secure, or just audited by a rubber-stamp firm?
Can the economic model withstand serious market stress, or will it collapse?
Is the team transparent and accountable, or are they anonymous ghosts?
When you start methodically evaluating these areas, you stop being a passive participant and become an informed investor. You gain the ability to tell a genuine opportunity from a well-disguised trap.
This simple workflow gives you a visual for the process. It's all about moving from identifying potential problems to putting protective measures in place.
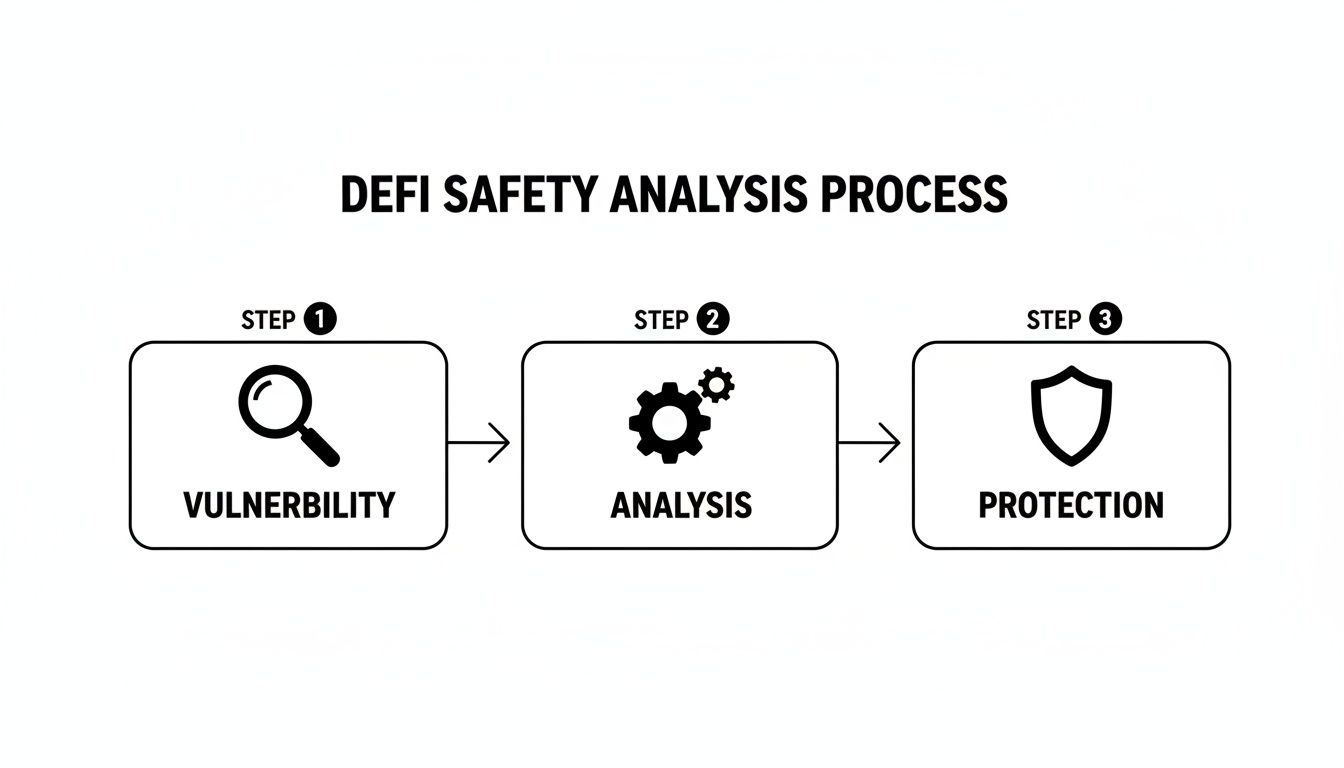
As the graphic shows, safety isn't a one-and-done deal. It's a continuous cycle of being vigilant and ready to respond.
The Real Cost of Neglecting Safety
The statistics out there are pretty alarming and really hammer home why this is so important. Just like safety data makes up 70-80% of the information in clinical trials, risk data should be the dominant factor in your DeFi investment decisions. It’s staggering to think that over 60% of the TVL on major chains has been hit by exploits at some point.
The financial ecosystem clearly has some major safety blind spots. Just looking at smart contract vulnerabilities alone, they led to a staggering $3.7 billion in losses back in 2022. There are some fascinating parallels between data-intensive safety studies and what we should be doing in DeFi.
This is where platforms like Yield Seeker come into play. They make this intense level of analysis accessible by automating these complex checks. By constantly monitoring for red flags and anomalies, they provide an institutional-grade defense, letting you focus on capturing yield without having to shoulder the entire burden of manual research yourself.
Decoding Smart Contracts and Technical Risk
At the heart of every DeFi protocol is its code. You don't need to be a developer to get a solid read on a protocol's safety, but you absolutely have to know how to spot technical red flags. This all starts with digging into a protocol’s smart contract audit history.

Think of an audit as a formal code review done by an outside security firm. It's like getting a home inspection before you buy a house—it points out all the existing flaws, from tiny cosmetic stuff to critical weaknesses that could bring the whole thing down. But remember, not all audits are created equal. The reputation of the firm doing the audit matters a whole lot.
Evaluating Smart Contract Audits
When you stumble upon a new protocol, the very first question you should ask is, "Who audited this?" You're looking for reports from top-tier firms known for being incredibly thorough, like Trail of Bits, OpenZeppelin, or ConsenSys Diligence. An audit from some unknown or anonymous firm? It carries way less weight.
Once you find the report, don't just see the checkmark and move on. You need to read it with a critical eye. I always focus on a few key areas:
Critical and High-Severity Findings: These are the vulnerabilities that can get a protocol completely drained. The big question is: did the team actually fix them? If you see an audit report with unresolved critical issues, that's a massive red flag.
Audit Scope: What parts of the code did they actually look at? Sometimes, a team will only get non-critical contracts audited, leaving the ones that hold all the user funds completely unchecked.
Date of the Audit: DeFi moves at lightning speed. An audit from two years ago might be totally irrelevant if the protocol has pushed significant updates since then.
You can usually hunt down this info in a project's official documentation or by asking around in their Discord. For a more detailed look at how to break these reports down, check out our guide on navigating smart contract security audits.
Beyond the Audit Report
An audit is just a snapshot in time, not some permanent seal of approval. A proper technical risk assessment means you have to keep monitoring things. A great place to start is the project's GitHub repository, which is a public window into their development activity.
A healthy GitHub shows consistent updates, bug fixes, and active conversations between developers. On the flip side, a repository that's been dead silent for months is a huge concern. It could mean the project is abandoned or the team just isn't maintaining the code, leaving it wide open to new threats.
The core idea here is continuous verification. A top-notch audit gets you in the door, but it's the ongoing development and transparency that keep a protocol secure over the long haul.
This really isn't that different from safety monitoring in other high-stakes industries. Huge protocols like Aave and Compound, which hold a combined $40 billion TVL in stablecoins, have risk thresholds built-in that are similar to what you'd see in clinical trials. When you look back at past incidents, a staggering 82% of DeFi exploits came from code flaws that could have been caught with a thorough analysis. You can dig deeper into these findings on safety monitoring if you're curious. It just goes to show how powerful a proactive technical review can be.
Uncovering a Protocol's Economic Vulnerabilities
A perfectly audited smart contract can still blow up in spectacular fashion if its underlying economic model is broken. This is an absolutely critical part of any real protocol safety analysis. We have to move beyond just looking at the code and dig into the real-world financial mechanics that are supposed to keep user funds safe.
The vulnerabilities here are often way more subtle than a simple bug, but they can be every bit as destructive.

What we're hunting for are the hidden risks in how a protocol values assets, manages its money, and pays its users. A massive Total Value Locked (TVL) number might look impressive on the surface, but it can also be a giant honeypot, tempting attackers who know how to exploit economic loopholes instead of just code.
Assessing Price Feed and Oracle Risks
Lots of protocols depend on oracles—basically, third-party services that pipe in external data, like asset prices, onto the blockchain. If this price feed gets compromised or manipulated, the whole protocol can be drained in minutes.
The infamous Mango Markets exploit is the classic textbook case. An attacker manipulated the price of the MNGO token, which let them borrow against massively inflated collateral, and poof... the money was gone.
When you're looking at a protocol, you have to ask these questions:
What oracle is it using? You want to see established, reputable providers like Chainlink or Pyth. They pull prices from tons of different sources, which makes them much harder to manipulate.
What's the actual price source? A protocol pulling its price from a single, low-liquidity decentralized exchange is just asking for a flash loan attack. It's a massive red flag.
Is there a fallback? What happens if an oracle goes haywire and reports a crazy price? A well-built system will have circuit breakers or other safeguards to prevent disaster.
A protocol's security is only as strong as its weakest data input. An insecure oracle is a backdoor for attackers to exploit an otherwise secure system.
Think of it like post-market safety studies for a new drug. The drug might pass all the initial trials, but you need ongoing monitoring to spot unforeseen risks once it's out in the wild. A protocol might launch with a solid model, but its economic safety needs to be constantly checked as markets and data feeds change.
Treasury Health and De-Pegging Dangers
A protocol’s treasury is its lifeblood. It funds development, pays the bills, and keeps the lights on. But how it's managed tells you a ton about its long-term chances of survival.
One of the biggest red flags is seeing a treasury held mostly in the protocol’s own native, and usually volatile, governance token. This creates the perfect setup for a death spiral. If the token price crashes, the treasury’s value evaporates, which kills confidence and sends the price crashing even further. Game over.
On top of that, many yield strategies rely on stablecoins, but they are not all created equal. The collapse of Terra's UST was a brutal lesson that even the biggest algorithmic stablecoins can de-peg from their dollar value with catastrophic results.
Your analysis has to look at the type of stablecoins being used. Is it a fully-backed stablecoin like USDC, or is it an algorithmic one with built-in de-pegging risk?
To help you keep track, here's a quick checklist for spotting these economic landmines.
DeFi Economic Risk Checklist
This table gives you a quick rundown of what to look for when evaluating the financial and economic health of a DeFi protocol. Green flags are good signs of a resilient system, while red flags are serious warnings that require a much closer look.
Risk Factor | What to Look For (Green Flag) | Warning Signs (Red Flag) |
|---|---|---|
Oracle Security | Uses reputable, multi-source oracles like Chainlink or Pyth. Has fallback mechanisms. | Relies on a single DEX with low liquidity for price feeds. No sanity checks on data. |
Treasury Composition | Diversified treasury with a healthy allocation to stablecoins (e.g., USDC, USDT) and major assets (ETH, BTC). | Treasury is >50% held in the protocol's own volatile, native token. |
Stablecoin Dependency | Primarily uses fully collateralized, reputable stablecoins. | Heavy reliance on algorithmic or unproven stablecoins with known de-peg risks. |
Incentive Model | Sustainable token emissions that reward genuine long-term users and liquidity providers. | Insanely high, short-term APYs funded by aggressive token printing (mercenary capital). |
Liquidation Engine | Robust, well-tested liquidation system that can handle extreme market volatility. | Liquidation process is slow, centralized, or has failed during past market crashes. |
By really digging into these economic factors, you get a much clearer picture of a protocol’s true financial strength. It helps you look past the flashy, advertised APY and understand the fundamental risks that could wipe out your investment overnight.
Reading the Signs with On-Chain and Social Data
A protocol's code and its economic model are huge pieces of the puzzle, but don't forget that the blockchain itself tells a story. A proper protocol safety analysis means learning how to read that story by digging into on-chain and social data to see what's really going on with a project. This is where you put on your digital detective hat.
The beauty of DeFi is its transparency. Metrics like user growth, how much money is moving around, and the concentration of large holders (whales) are all out there for anyone to see. The real skill is knowing how to interpret this data to tell the difference between real, organic activity and just a bunch of manufactured hype.
Analyzing Key On-Chain Metrics
Tools like Dune Analytics and Nansen are your best friends here. They let anyone build dashboards and keep an eye on a protocol's vital signs. When I’m checking out a new opportunity, I always start with a few core indicators to get a feel for the real flow of capital and user engagement.
User Growth: Are new wallets consistently interacting with the protocol over time? A sudden, massive spike might just be a sign of a short-term incentive that's attracting mercenary capital. Those users will likely disappear the second the rewards dry up.
Transaction Volume: High volume can look great on the surface, but you have to dig a little deeper. Is a handful of whale wallets driving most of the activity, or is it spread out across a wide base of actual users? The latter is a much healthier sign.
Whale Concentration: If a protocol is dominated by a few massive holders, that's a major red flag. These whales can pull liquidity or dump tokens in an instant, crashing the price and leaving everyone else holding the bag.
For anyone who wants to get their hands dirty with on-chain analysis, getting good with tools for understanding blockchain explorers is non-negotiable. These let you follow the money and verify transactions yourself.
We cover more strategies for using this kind of data in our complete guide to on-chain risk management.
The Human Element: Social Signals
Beyond the raw numbers, you can't ignore the human element. The vibe in a project's community on Discord and Twitter can tell you a lot about its long-term chances.
A vibrant, engaged community with developers who actually talk to people? That's a massive green flag. On the flip side, if the community is just bots, generic hype posts, and questions that go unanswered for days, you should probably run the other way.
This isn't so different from how surveillance works in other high-stakes fields. Think about medicine, where post-marketing systems collect millions of reports to find safety signals. In DeFi, we have platforms like Rekt.news that track exploits. Their data shows a staggering $1.8 billion was lost across 150 incidents in 2024 alone, with 65% of that happening in stablecoin protocols.
A healthy protocol has both strong on-chain fundamentals and a thriving, transparent community. When the data on the blockchain aligns with positive social signals, you have a much stronger basis for trusting the project's safety and potential.
How AI Automation Changes the Game for Protocol Safety
Manual analysis is great for getting a fundamental understanding of a protocol, but it’s just a snapshot in time. The DeFi market never sleeps, and major risks can pop up in a matter of seconds. This is where AI-driven automation completely flips the script on protocol safety analysis, taking us from periodic check-ins to constant, real-time vigilance.

Automation isn't about replacing human expertise; it's about amplifying it with speed and scale that are just not humanly possible. Platforms like Yield Seeker are built to run the same rigorous checks we've discussed—from smart contract monitoring to economic stress tests—but they do it around the clock.
This constant oversight is a massive advantage. Think about a protocol's treasury suddenly shifting its composition toward its own volatile native token—a huge red flag. A manual analyst might spot this in their weekly review, but an automated system can flag it the moment it happens on-chain.
Real-Time Threat Detection and Response
The biggest win with automation is its ability to chew through immense amounts of data in real time. An AI agent can keep an eye on thousands of on-chain data points across dozens of protocols at once, something no team of humans could ever hope to match. This kind of capability is core to modern security. If you're curious about how new tech is bolstering security, it's worth reading up on the role of Artificial Intelligence in enhancing cybersecurity.
This non-stop monitoring translates directly into practical safety measures:
Instant Anomaly Detection: AI algorithms are trained to spot weird transaction patterns, sudden liquidity drains, or oracle price deviations that are often the first signs of an exploit.
Automated Economic Stress Tests: These systems can constantly run simulations of market crashes or de-pegging events to see how a protocol holds up, updating its risk score on the fly.
Proactive Fund Reallocation: If a risk level you've set gets breached, an automated system can immediately move funds to a safer, pre-vetted protocol. It's about protecting your capital before a crisis hits, not after.
It's a bit like post-authorization safety studies in medicine, where systems continuously monitor for adverse events after a product hits the market. In DeFi, automation gives us that same crucial, ongoing surveillance.
Automation transforms protocol safety from a reactive, forensic exercise into a proactive, preventative discipline. It’s about detecting the storm before it hits, not just analyzing the wreckage afterward.
Making Advanced Safety Accessible to Everyone
Not long ago, this level of deep, continuous analysis was a luxury reserved for big funds with teams of dedicated analysts. AI-powered platforms are changing that by putting institutional-grade tools into the hands of everyday users.
With platforms like Yield Seeker, you get the benefits of a sophisticated safety framework without having to run every check yourself. Automation connects all the dots—technical, economic, and on-chain—to give you a holistic and dynamic picture of risk. To see how these systems operate in the wild, you can learn more about automated risk assessment tools and how they're applied.
The end goal is simple: to achieve risk-aware yield with confidence. Automation takes away the constant burden of manual research, letting you allocate your capital efficiently while an AI agent handles the tireless, 24/7 job of monitoring and protection. It makes a truly robust safety strategy not just possible, but practical for everyone.
Got Questions About Protocol Safety?
Diving into DeFi safety can feel like navigating a maze. It’s natural to have questions. This section is all about giving you direct, no-fluff answers to the things people ask most, helping you build a smarter, more robust protocol safety analysis framework.
What's the Single Most Critical Factor in a Protocol Safety Analysis?
If there's one thing you absolutely cannot compromise on, it's a protocol's smart contract audit history. An unaudited protocol should be an immediate, non-negotiable red flag. Always hunt for recent audits from reputable security firms that cover every single core contract handling user funds.
But an audit is just a snapshot in time—a clean bill of health on the day it was done. It's not a permanent shield. This is exactly why continuous monitoring of a protocol's technical, economic, and on-chain health is so vital for long-term security. A good audit gets a protocol in the door; ongoing vigilance keeps it safe.
Can a Protocol with High TVL Still Be a Huge Risk?
Absolutely. In fact, a high Total Value Locked (TVL) can create a dangerous false sense of security. While it definitely shows user trust and adoption, it also paints a giant bullseye on the protocol, making it a far more attractive target for hackers.
Some of the biggest and most devastating DeFi exploits in history happened on protocols with massive TVL. You have to weigh TVL against other critical factors like audit quality, team transparency, and the soundness of its economic model.
Never assume high TVL automatically means low risk. A bigger honeypot just attracts more sophisticated attackers, which makes a thorough protocol safety analysis even more critical, not less.
How Does Automated Monitoring Stack Up Against a Manual Check?
A manual check is like taking a photo. It’s a static snapshot of a protocol's health at one specific moment. It's fantastic for a deep dive, but it's already out of date the second you finish it.
Automated monitoring, like the systems we've built at Yield Seeker, is a dynamic, 24/7 surveillance system. It's constantly scanning for a whole range of threats in real time.
This includes things like:
On-chain weirdness, like sudden, massive withdrawals.
The first signs of a liquidity crisis or a potential bank run.
Governance attacks right as they start to form.
Suspicious smart contract interactions that don't fit normal patterns.
This real-time vigilance allows an automated system to spot and react to threats as they emerge—something that's just impossible for a human analyst to do around the clock. It shifts safety from a periodic chore to a constant state of readiness.
Is It Possible to Have Zero Risk in DeFi?
Nope. Chasing zero risk in DeFi is a fool's errand. The entire ecosystem is built on rapid innovation and experimentation, and that inherently comes with a mix of smart contract, economic, and operational risks.
The real goal of protocol safety analysis isn't to find some mythical risk-free investment. It’s to help you understand, measure, and intelligently manage potential threats. A solid analysis gives you the power to minimize your exposure to preventable losses and make much smarter decisions about where you put your capital. It's all about managing risk, not pretending it doesn't exist.
Ready to put automated protocol safety analysis to work for you? Yield Seeker uses AI to continuously monitor and allocate your stablecoins to competitive, risk-aware yield opportunities. Start earning smarter at https://yieldseeker.xyz.