
Secure yield automation is all about using smart contracts and AI-driven platforms to make passive income from your stablecoins, but—and this is the important part—while keeping a close eye on security. It's a blend of automated capital allocation and real-time threat analysis, designed to sniff out the best risk-adjusted returns in decentralized finance (DeFi) without you having to be glued to your screen 24/7.
This isn't about chasing those crazy, unsustainable triple-digit yields. It’s a shift towards building consistent, safer growth over the long haul.
The Foundations of Automated DeFi Yield

Let's be clear: true secure yield automation isn't some magic money machine. It’s a methodical system built on three core pillars that work in tandem to grow your capital while protecting it. Getting your head around these components is the first step to building a passive income strategy in DeFi that actually lasts.
At its core, the system is designed to tackle the two biggest hurdles for most people: the insane amount of time it takes to do proper research and the emotional decision-making that almost always leads to chasing risky, overhyped assets.
Automated Smart Contract Interactions
At the heart of it all, automation in DeFi just means using software to handle transactions for you. Instead of you manually shuffling funds between lending protocols or liquidity pools, an automation platform does the heavy lifting based on a strategy you've set.
This brings a few huge advantages:
Speed: Capital can be shifted in seconds to jump on a brief opportunity or, more importantly, to get out of a risky position way faster than any human could.
Efficiency: It completely removes the need to constantly monitor dashboards and burn gas on every little adjustment. That saves you both time and money.
Consistency: The strategy just runs, 24/7, without getting greedy or fearful. It just sticks to the rules.
Think of it like setting up a list of instructions for your money. For example, a rule could be as simple as, "always keep my USDC in the top three audited lending protocols, and rebalance weekly to whichever one has the highest stable rate."
Real-Time Risk Analysis
Automation without solid security analysis is just a faster way to get rekt. This is where the modern platforms really stand apart. They build in continuous risk monitoring that scans for threats before and after your money is deployed.
This means checking for common smart contract bugs, like reentrancy vulnerabilities or shoddy access controls. It also means keeping an eye on market conditions, like a stablecoin starting to wobble off its peg or a protocol's liquidity suddenly vanishing.
A key evolution in DeFi security has been the shift from periodic audits to continuous, automated threat detection. It's no longer enough for a protocol to be safe on day one; it must remain safe every single day after.
Dynamic Capital Allocation
The final piece of the puzzle is linking the automation with the risk analysis. Dynamic allocation means the system doesn't just "set and forget." It's actively managing your funds. If a protocol's risk score suddenly spikes or a better, safer opportunity pops up somewhere else, the platform automatically moves your funds.
This is where AI has been a game-changer. Using AI as a sort of 'financial co-pilot' has completely transformed secure yield automation. These systems can now scan smart contracts for vulnerabilities in real-time and even explain the risks of a liquidity pool in plain English. This shift helped the DeFi market grow up from the wild days of 'DeFi Summer' into a more stable infrastructure, with Total Value Locked (TVL) climbing back to $130–$140 billion in early 2026 from the lows after the FTX collapse. If you're curious, you can learn more about how DeFi has evolved since 2020 and where it's headed.
Building Your Personal DeFi Security Framework

Before you even think about deploying a single dollar, you need to build a personal security framework. This is about more than just picking good protocols; it's about creating a solid operational structure that shields you from the very real dangers in DeFi, whether it's a smart contract bug or your own mistake.
The truth is, true secure yield automation begins with a defense-in-depth mindset.
We're going to move past the theory and get into the practical, nitty-gritty steps that actually protect you from the most common threats. I’m talking about protocol exploits, economic meltdowns like a stablecoin de-pegging, and simple, costly human error. Each one of these requires a specific, actionable defense.
The idea is to bake a security-first approach into everything you do. This isn't a one-and-done setup; it's an ongoing practice that will become the bedrock of your success in automated yield farming.
Fortify Your Foundation with Hardware Wallets
Your first line of defense is totally non-negotiable: get a hardware wallet. This little device keeps your private keys completely offline, which makes it practically impossible for malware or a phishing scam on your computer to drain your main stash of funds. Think of it as your personal digital vault.
Any significant amount of capital—the funds you aren't actively using for daily transactions—needs to live on this device. This separation is the single most important security step you can take. If you skip this, you’re basically leaving the front door to your entire portfolio wide open.
Implement a Hot Wallet Strategy
For the day-to-day stuff, like interacting with DeFi protocols, you'll want a dedicated "hot wallet." This is just a browser-based wallet, like MetaMask or Rabby, that you use to connect to dApps and sign transactions. The golden rule here? Keep the balance low.
Treat this wallet like the cash you carry around with you—only hold what you'd be okay with losing. If this wallet ever gets compromised, the damage is contained, and the vast majority of your assets are still safe and sound in your hardware wallet.
Actionable Tip: I recommend setting a strict limit for your hot wallet. For instance, never keep more than 5% of your total DeFi portfolio in it. If you need to make a large deposit into a protocol, transfer the funds from your hardware wallet right before you make the transaction, and don't let a large balance just sit there afterward.
This simple two-wallet system massively reduces your attack surface. You're separating your long-term savings from your daily spending, which is a core principle of good operational security.
Assess Smart Contract and Economic Risks
Even if your personal security is locked down tight, you're still exposed to risks at the protocol level. Not all DeFi platforms are built the same, and knowing how to vet them is a critical skill for secure yield automation.
The biggest mistake you can make in DeFi is assuming a high yield means it’s a quality protocol. More often than not, it's a sign of uncompensated risk, whether that’s from unaudited smart contracts or a shaky economic model.
When you're looking at a new yield source, your due diligence should hit a few key points:
Smart Contract Audits: Look for multiple audits from well-known security firms. A single audit just doesn’t cut it anymore; you want to see a consistent history of commitment to security. You can go deeper on this by checking out our guide on how smart contract risk scoring works.
Team Transparency: Is the team public and doxxed? Anonymous teams are a massive red flag for a potential rug pull. You want to see active communication, a clear roadmap, and a professional public presence.
Economic Sustainability: Ask yourself, where is the yield actually coming from? If it's just from printing more of their own token, that's not sustainable. Real, healthy yield comes from genuine economic activity, like fees from lending, trading, or other services people are actually using.
Your final layer of defense is diversification. Don't throw all your stablecoins into one protocol, or even into a single type of yield. By spreading your capital across different primitives—like lending, providing liquidity, and staking—you build a much more resilient portfolio that can handle one part of your strategy failing without taking everything down with it.
How to Select the Right Protocols and Chains
The DeFi ecosystem is a chaotic maze. Thousands of protocols are scattered across dozens of blockchains, and picking the right spot to park your capital for secure yield automation is the single most critical decision you'll make.
This isn't just about chasing the highest APY. It's about finding battle-tested venues that are built to last and won't vanish overnight. You need a systematic way to vet these opportunities, almost like a professional risk analyst. It's this exact kind of rigorous, 24/7 analysis that platforms like Yield Seeker automate, but understanding the core principles yourself is crucial.
Analyzing Protocol Quality and Security
Your first layer of due diligence starts at the protocol level. Before you even think about connecting your wallet, you have to dig into the fundamentals. A high Total Value Locked (TVL) often gets thrown around as a proxy for trust—after all, it means other people have put their money there. But TVL can be a vanity metric, easily inflated by unsustainable token rewards.
You need to look for stronger signals of a protocol's commitment to security.
Audit History: Look for a history of multiple, recent security audits from reputable firms. A single audit from a year ago just doesn't cut it. A quality protocol will have an ongoing relationship with security researchers, showing they're serious about proactive defense.
Team Transparency: Is the founding team public and doxxed? Anonymous teams are a massive red flag in this space. You want to see builders with a track record and a history of clear, professional communication with their community.
Yield Sustainability: Always ask, "Where is the yield actually coming from?" If the answer is just printing a native governance token out of thin air, that model is a ticking time bomb. Real, sustainable yield comes from tangible economic activity, like fees from lending or commissions from trading.
A protocol's real strength isn't measured by its peak APY, but by how it holds up during a brutal market downturn. Look for protocols that have survived multiple cycles and kept their users' trust through it all.
Take a look at a platform like Aave, which boasts over $55 billion in cross-chain dominance. It's become a foundational pillar of DeFi for a reason: it has consistently chosen security and sustainable economics over short-term hype. This is why automated strategies naturally gravitate towards these established players.
Protocol and Chain Evaluation Checklist
To make this process more concrete, here's a checklist you can use to systematically evaluate protocols and the blockchains they live on. Think of it as a scorecard to cut through the noise.
Evaluation Criteria | What to Look For | Red Flags |
|---|---|---|
Security Audits | Multiple, recent audits from top-tier firms. Public bug bounty program. | No audits, outdated audits, or audits from unknown firms. |
Team | Public, doxxed team with a proven track record in Web3. | Anonymous team, lack of communication, questionable history. |
Yield Source | Yield generated from real economic activity (lending, trading fees). | Yield comes entirely from inflationary token emissions. Unsustainably high APYs. |
Total Value Locked (TVL) | Consistent, organic growth over time. Resilient during market dips. | Sudden, massive spikes in TVL driven by hype. Rapid TVL collapse. |
Community & Docs | Active, engaged community. Clear, comprehensive documentation. | Ghost town Discord. Poor or non-existent documentation. |
Blockchain Security | Operates on a secure, decentralized L1 or a reputable L2 with strong L1 ties. | Runs on a highly centralized or unproven new chain with no track record. |
This checklist isn't exhaustive, but it provides a solid framework for making more informed decisions and avoiding the most common pitfalls.
Choosing the Right Blockchain Network
Once you've shortlisted some promising protocols, you have to think about the blockchain network they're built on. The choice between an established Layer 1 (L1) like Ethereum and a newer Layer 2 (L2) like Base comes with very different trade-offs that directly affect your security and profitability.
Layer 1s (e.g., Ethereum): Offer maximum security, backed by the full decentralization of the main chain. The downside? Transaction costs can be painfully high, eating into your profits, especially for smaller, more frequent automated actions.
Layer 2s (e.g., Base, Arbitrum): Provide drastically lower transaction fees, which is a huge advantage for automation. This allows for more frequent rebalancing and compounding, which can seriously boost your net returns over time. The trade-off is that these ecosystems are newer and may have fewer battle-tested protocols and less overall liquidity.
For most secure yield automation strategies focused on stablecoins, L2s have become the clear winner. The cost savings are just too significant to ignore. The key is to stick with L2s that have a strong connection to a secure L1 and are seeing rapid growth in their own high-quality ecosystem. For a deeper dive, check out our piece on protocol diversification strategies across different chains.
The DeFi landscape is always shifting. Some analyses predict that by 2026, strategic automation will be a necessity to navigate lower returns and increasing risks like smart contract exploits. As the market matures and regulatory frameworks like the 1099-DA form take shape, investors are increasingly turning to AI-driven tools for smarter, risk-aware allocation. You can get a better sense of these trends by reading about how automation is shaping the future of yield farming.
This rigorous, multi-layered vetting process—checking the protocol's security, the team's credibility, the yield's source, and the underlying chain—is fundamental. It's a lot of work, but it's a necessary step that automation platforms like Yield Seeker handle continuously to make sure your capital is deployed intelligently.
Your Workflow for Setting Up Automated Yield
Alright, theory's out the window. It's time to get our hands dirty and walk through the actual process of setting up a secure yield automation strategy. We'll go from the initial wallet setup right up to the moment your personal AI agent takes the wheel.
The whole point here is to show you how a few smart, upfront moves can unlock a powerful, hands-off system that works for you 24/7.
Before we jump into the DeFi-specifics, it’s helpful to have a grasp of what is workflow automation in general. Understanding the core idea makes it clearer why we’re building things this way. For our example, we'll use a platform like Yield Seeker since it’s designed to make this whole thing easier, but the principles are the same no matter what tools you use.
Beginning With Wallet Setup and Funding
First things first: your digital wallet. Think of this as your personal bank vault and the key to everything in DeFi. For a truly secure setup, you absolutely need two things: a hardware wallet for your main stash and a "hot" browser wallet for your day-to-day moves.
Your first job is to get this setup funded with stablecoins like USDC.
Buy Your Stables: Grab some USDC from a reputable, regulated exchange. This is easily the safest and most straightforward on-ramp for most people.
Move to Cold Storage: The moment the purchase clears, transfer the bulk of your funds off the exchange and onto your hardware wallet. This is non-negotiable for security. Never, ever leave a large amount of capital sitting on an exchange.
Fund Your Hot Wallet: From your hardware wallet, send a smaller, operational amount of USDC over to your browser wallet (like MetaMask). This is the cash you'll actually use for your first deposit.
This two-wallet approach is critical. It means that even if your browser wallet somehow gets compromised, your primary capital is safe and sound, completely offline.
Connecting to an Automation Platform
With your wallet funded and ready to go, the next step is linking up with your automation platform of choice. Modern platforms like Yield Seeker have made this part incredibly simple and secure. They use standard wallet connectors that never ask for, or see, your private keys.
You'll usually just head to the platform's site and hit a "Connect Wallet" button. This will pop open your browser wallet, asking for permission to connect to the dApp (decentralized application). It’s super important to understand what you're actually approving here: you are only letting the site view your wallet address and balances. You are not giving it permission to spend your money.
Security Tip: Always, always double-check the URL of any site you're connecting your wallet to. Scammers are experts at creating copycat websites with almost identical domain names to trick you into signing malicious transactions.
Once you’re connected, you’ll land on the user dashboard. This is your mission control. From here, you can see your balances, check out different strategies, and watch your earnings in real time.
This is a simplified look at the kind of vetting process a high-quality automation platform runs behind the scenes, constantly, on your behalf.
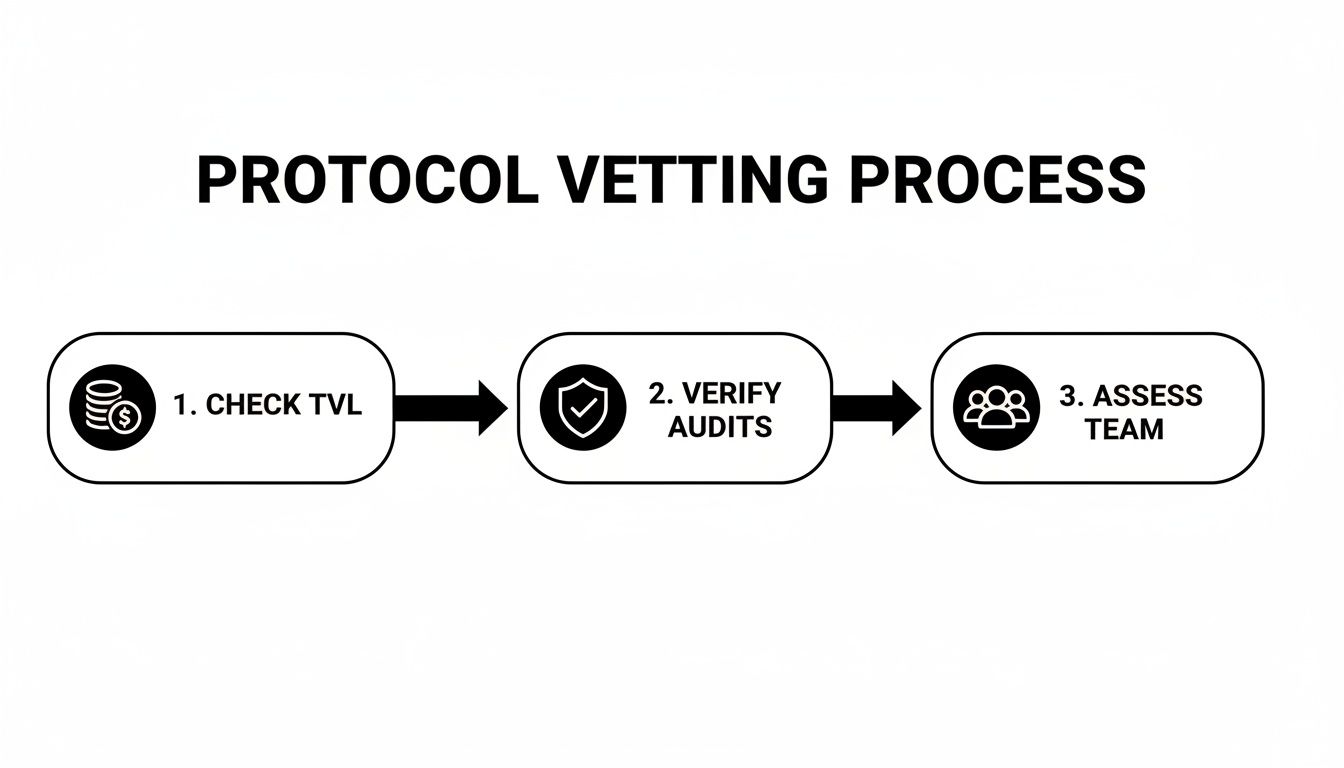
This process highlights the layers of due diligence—from checking liquidity and audits to assessing the team—that are the foundation of any secure strategy.
Making Your First Deposit and Activating Automation
Now for the fun part: putting your capital to work. The deposit process itself is designed to be dead simple. You'll enter the amount of USDC you want to deposit and then be asked to sign two transactions from your hot wallet.
The Approval Transaction: This is a standard DeFi practice. You're giving the platform's smart contract permission to interact with a specific amount of your USDC. It's a key security feature that keeps you in the driver's seat—the contract can never touch a penny more than you authorize.
The Deposit Transaction: This is the final step. It moves your USDC from your wallet into the platform's strategy contract, and just like that, your position is live.
As soon as your deposit is confirmed on the blockchain, the system takes over. If you’re using a platform like Yield Seeker, this is where your personalized AI agent clocks in. It immediately starts scanning the market, analyzing risk-adjusted yield opportunities across a pre-vetted list of protocols.
From this moment on, the secure yield automation is officially running. The AI agent handles the heavy lifting without you needing to do anything else:
Continuous Monitoring: It's watching protocol health, market conditions, and yield rates 24/7.
Dynamic Reallocation: It automatically moves your capital between different protocols to chase the best returns while staying inside your risk limits.
Automated Compounding: It reinvests your earnings back into your principal, putting the power of compounding on autopilot to accelerate your growth.
Your role now shifts from being an active trader to a strategic overseer. You can pop into your dashboard anytime to track performance, see your earnings pile up, and relax, knowing a sophisticated system is managing all the complexity for you.
Keeping a Watchful Eye on Your Automated Strategy
Automation is a game-changer, but it’s definitely not a "set it and forget it" magic button. I've seen too many people make that mistake. While the AI agent handles the daily grind of shifting funds, you still need to keep a high-level view of what's happening. Think of it like this: you're the CEO, and your agent is the super-efficient operations manager. You don't need to micromanage, but you absolutely need to check in on the key metrics to make sure everything is running smoothly.
This is all about maintaining strategic oversight. Good continuous monitoring gives you the peace of mind that your capital is not only working hard but also staying safe.
Focus on the Metrics That Actually Matter
When you log into your dashboard, it's easy to get bogged down by a ton of data. Most of it is just noise. To really understand how your secure yield automation strategy is performing, you have to zero in on a few key performance indicators (KPIs) that tell the whole story.
Here's what I always look at:
Net APY (After Fees): This is the number that counts. A protocol might flash a huge APY, but what actually lands in your account after platform fees and gas costs? That's your true return.
Total Return in USD: APY is great for comparison, but seeing the actual dollar amount your investment has generated keeps things grounded. This is the real-world growth of your initial capital.
Current Asset Allocation: You need to know exactly where your funds are at all times. If you glance at your dashboard and see that 80% of your capital has suddenly piled into a single, brand-new protocol, that’s something you want to be aware of immediately. Transparency here is non-negotiable.
For a much deeper dive into the specific tools and metrics we use, check out our guide on how to go about implementing real-time yield monitoring for your own strategies.
Have an Emergency Exit Plan Before You Need One
DeFi is still the wild west in many ways. Black swan events happen—a major protocol gets exploited, a stablecoin de-pegs, you name it. This is why having a clear, rehearsed emergency withdrawal plan is absolutely critical. You don't want to be fumbling around trying to figure out how to pull your funds when the market is in a panic.
Your plan should be dead simple:
Define Your Triggers: What event would make you pull the plug? It could be a specific news headline, a protocol's TVL dropping by over 50% in 24 hours, or a stablecoin wobbling more than 1% off its peg. Decide this now.
Practice the Process: Seriously, do a dry run. Know exactly which buttons to click to get your funds out of the automation platform and back into your own wallet. In a real crisis, every second counts.
Plan Your Next Move: Once the funds are back in your wallet, what's next? Swap to a different stablecoin? Bridge to another chain? Move it to Coinbase? Figure this out ahead of time so you're not making panicked decisions.
When everything is hitting the fan, the most valuable feature isn't a high APY—it's instant liquidity. Your ability to access your funds without any lock-ups or penalties is the bedrock of a truly secure strategy.
We built Yield Seeker around this very principle. There are no lock-up periods and no withdrawal fees, ensuring you always have the final say over your capital. This isn't just a convenience; it's a critical safety feature. The DeFi market has seen a solid recovery, with total value locked finding a floor around $130–$140 billion in early 2026 after the FTX mess. In this more mature environment, automated platforms are becoming essential for finding stable returns, with some strategies consistently hitting yields near 5% on stablecoins. Staying prepared is how you navigate this world safely.
Common Questions About Secure Yield Automation
Jumping into automated DeFi can feel like a big leap, and it’s natural to have questions. Concerns about security, how much control you actually have, and the sheer complexity of it all are completely valid. Let's tackle some of the most common ones I hear to clear things up.
The idea here isn't to brush off concerns but to give you straight, honest answers. Getting your head around these points is the key to building a strategy you can feel confident about.
Is My Money Ever Locked Up?
This is usually the first question people ask, and for good reason. The answer should always be a hard no. Any legitimate yield automation platform has to put your liquidity and control first. Your capital should never, ever be locked into some fixed-term contract you can't get out of.
Things in DeFi can change in a heartbeat. A major protocol might get hit with a critical bug, or a stablecoin could start to wobble. In those moments, the ability to pull your funds out immediately is your single most important safety net.
Any platform that forces mandatory lock-up periods or slaps you with huge withdrawal penalties is adding a massive, unnecessary risk. Always stick with services that let you deposit and withdraw on your own terms, 24/7. That flexibility is a non-negotiable part of a good security model. It ensures you're always in the driver's seat.
How Does Automation Handle Security Risks?
This is where you can tell the difference between a smart platform and a reckless one. A naive automation tool just chases the highest APY it can find, which often means blindly jumping into unaudited, sketchy protocols. Sophisticated automation, on the other hand, is built with security as its foundation.
Relying on automation without rigorous, continuous human oversight is a recipe for disaster. The best systems blend AI-driven efficiency with expert human judgment. You can't just outsource security vetting to an algorithm that might have flawed or outdated training data.
A truly secure system uses a defense-in-depth approach:
A "Walled Garden" of Protocols: The automation should only be allowed to operate within a pre-vetted list of protocols. This means a human team has already done the heavy lifting—checking for multiple security audits, making sure the team is transparent, and confirming the tokenomics are sustainable.
Real-Time Health Checks: The platform needs to be constantly monitoring the health of these approved protocols. This means watching for weird transaction volumes, sudden drops in liquidity, or even chatter on social media that might signal a problem.
Built-in Circuit Breakers: Smart systems have emergency stops. If a protocol's risk score suddenly spikes past a certain point, the automation should be programmed to automatically pull funds to a safe spot until a human can assess what’s going on.
This model lets technology handle the day-to-day work of allocating capital for efficiency, but the big-picture security decisions are still governed by sound, conservative principles. It’s about using tech to execute a safe strategy, not to invent a risky one.
Is This a "Set and Forget" System?
While automation slashes the daily workload, it's a mistake to think you can just turn it on and walk away forever. The most successful users I've seen adopt a "trust but verify" mindset. They let the automation do the tedious stuff like rebalancing and compounding, but they still keep a strategic eye on their investment.
This means you should probably plan to:
Glance at Your Dashboard Regularly: A quick check-in a few times a week is a great habit. Just look at your net returns, see where your assets are allocated, and check for any notifications.
Keep a Pulse on the Market: You don't need to become a full-time crypto analyst. But having a general sense of major market trends will help you understand why the automation is making certain moves.
Revisit Your Goals: Every so often, take a step back and ask if the strategy still lines up with your financial goals and risk tolerance. What worked for you six months ago might need a small tweak today.
Think of yourself as the pilot of a modern airliner. The autopilot does most of the flying, but the pilot is always there, monitoring the systems and ready to take the controls if needed. That’s the perfect relationship to have with your automated yield strategy—you get the best of both worlds: efficiency and control.
Ready to put your stablecoins to work with an AI co-pilot? Yield Seeker offers a secure, transparent, and effortless way to earn automated yield in DeFi. Your AI Agent handles the complexity while you stay in control. Start earning smarter today at yieldseeker.xyz.